Articles
One of the most obvious customer modules is the Customized Menu element, and this replaces Minecraft’s standard identity display screen which have ThunderHack-Recode’s individualized user interface. Customer modules in the ThunderHack-Recode have the effect of controlling the buyer-front features and you can consumer experience unlike myself modifying game play mechanics. KillAura are a tool one instantly attacks other participants or mobs in the online game, providing the player an unfair virtue within the combat. These resources are created to end up being recyclable across additional combat segments, making sure uniform capability and you will reducing code replication. Instead of the fresh segments themselves, which offer prevent-member abilities, these tools provide reusable password components you to deal with complex handle-associated computations and operations.
— fabric-api-lookup-api-v1 step one.6.50+82b1bb3e4f
Some have also quoted numerous clues on the password for example a hidden reference to the keyword MYRTUS, believed to make reference to the brand new Latin name myrtus of your Myrtle tree, that Hebrew is known as hadassah. The device can be regarding the Us, and that acquired P-1s of Libya’s former atomic program. Professionals accept that Israel along with somehow gotten P-1s and you will tested Stuxnet to the centrifuges, hung during the Dimona studio that’s element of its very own nuclear system. Israel has not yet in public places stated on the Stuxnet attack but in 2010 affirmed you to definitely cyberwarfare are now among the pillars of the defense doctrine, that have an army cleverness unit set around pursue each other defensive and you can offending options.
— fabric-registry-sync-v0 4.0.20+ee30b13a4f
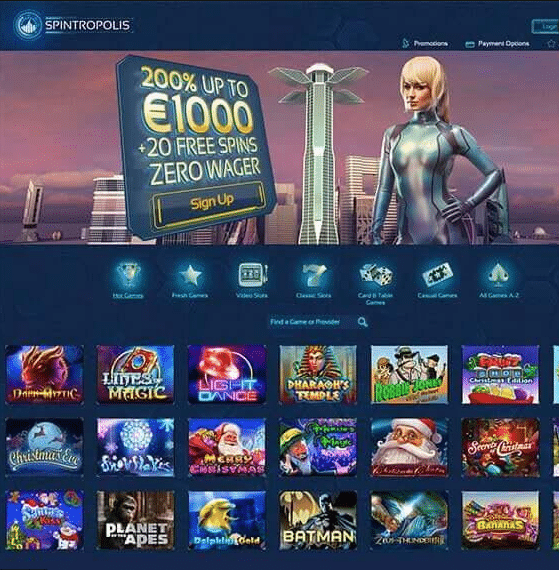
I strongly recommend your better 5 cheats so you can earn facing Thunderstruck Position cheat. “With respect to the email address our very own cyber benefits provided for the organizations, they think a good hacker device Metasploit was utilized. A computer trojan might be the reason for Ac/DC involuntarily blasting in the limit frequency in the a nuclear facility within the Iran, reports Gawker. He says the new Air-con/DC assault on the Islamic Republic’s Nuclear Department is relayed to help you your from the an Iranian scientist. The new widespread stream out of password forced the new centrifuges to help you spin away from manage, wrecking everything in the method.
What’s more, it installs a great rootkit – the initial including reported situation on this program – you to definitely hides the fresh virus to your system and you can masks the alterations inside the rotational rates out of monitoring systems. The brand new virus and used a no-date exploit regarding the WinCC/SCADA database app when it comes to a hard-coded database code. https://vogueplay.com/uk/ted-bingo-casino-review/ The fresh virus may be able to modify the password on the PLC gadgets undetected, and you can after that in order to cover-up their exposure away from WinCC should your control software tries to understand a contaminated stop from memories in the PLC system. Considering specialist Ralph Langner, once mounted on a windows system, Stuxnet infects enterprise files belonging to Siemens’ WinCC/Pcs 7 SCADA control application (Step 7), and you can subverts an option communications collection out of WinCC entitled s7otbxdx.dll.
Abreast of typing a machine the very first time, you are offered a person-friendly buyer settings monitor. There is certainly indeed an instructions tips guide of forms on the internet based on how so you can replicate the newest hack. Depending on the Brink, hacking somebody’s pc to enjoy sounds as a result of there audio system isn’t as tough as it may looks.
Israel
Frequently the federal government-sponsored hackers believe a similar, and you will apparently chose to great time ACDC’s ‘Thunderstruck’ from the full regularity thanks to Iranian computers while they put the world’s atomic program right back decades. Certain technology and you will cybersecurity businesses, in addition to Google, and also the email cybersecurity business Proofpoint have told NBC Reports one to he has largely viewed Iran’s hackers carrying out espionage linked to the battle. Despite the You and Israel’s bombardment away from Iranian bodies organization, Wednesday’s deceive showed that Tehran continues to have hackers ready inflicting destroy, cybersecurity analysts said. Iran-connected hackers got mainly hushed in terms of episodes to the United states teams because the battle first started history few days.
Uncharted: Crime and Havoc on the Music business
You to definitely wasn’t all of the hackers drawn, appear to. ThunderHack-Recode is a sophisticated Minecraft consumer which have a standard, event-driven structures. The consumer uses Fabric’s Mixin system so you can inject password for the Minecraft kinds during the runtime. That it enjoy-motivated buildings allows the client to change Minecraft’s decisions dynamically as opposed to thorough code changes. The customer utilizes a meeting-centered buildings to change Minecraft’s conclusion as opposed to myself editing the bottom games password. So it file provides an overview of the new buyer’s tissues, core solutions, and you will fundamental framework principles.

Back into 2012, there had been really serious concerns you to definitely Iran is near to development the very own atomic guns. It was allowed to be 20 minutes as the powerful since the Stuxnet, and that, this season, caused particular Iranian nuclear centrifuges to help you fail. Fire is recognized as the “the most advanced cyber malware ever before” whether it strike systems inside Iran and you can along side Middle eastern countries in-may. Which is also to your Wednesday, your head from Iran’s It and you can Correspondence Team, Ali Hakim Javadi, recommended the fresh Us to condemn arranged cyber symptoms.

